If you’re teaching reflected cross-site scripting to a newbie, what could be a classic example?
A search page taking search keyword as input and reflecting it back on the result page, along with the search results.
I logged into ICICI Bank website after ages and noticed a new search page on my dashboard. Out of curiosity, I just wanted to check if they were encoding the input properly. I entered a few special characters in the search field and right clicked on the result page to view the HTML source but an alert popped up stating that ‘Due to security reason, right click is not allowed’. It is generally very trivial to bypass such client side restrictions and I don’t think any site needs to do that as a security control.
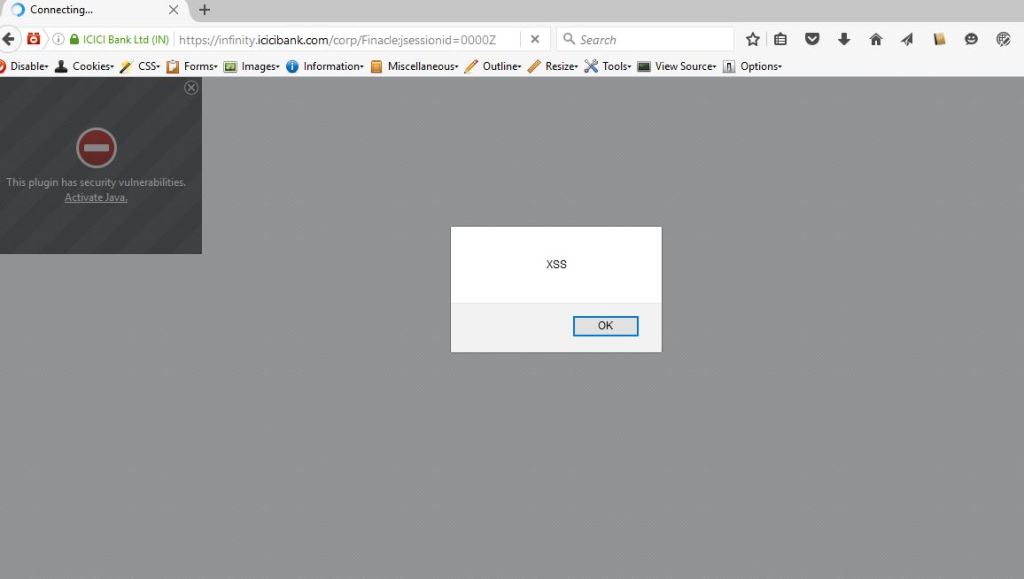
I just added ‘view-source:’ before the URL and was able to see the generated HTML source. After looking at the HTML source, I worked on the XSS payload and below payload successfully popped up an alert, confirming the presence of Cross-Site Scripting vulnerability.
xxx')</script>alert("XSS")
Timeline:
07/31/2016 – Reported this issue to ICICI’s anti-phishing email and whatever other emails I was able to find. Also shared the screenshot and steps to reproduce the issue.
08/02/2016 – Received a generic reply from their customer care asking for my account details and phone number to help me further.
08/02/2016 – Requested them to forward that email to their IT Security team or to anyone responsible for the IT department.
08/26/2016 – Asked for an acknowledgement or an update. Received a generic email from someone in customer care department.
03/05/2017 – Requested for an update.
01/18/2018 – After some good time, when I logged in to the ICICI site, I noticed that XSS was fixed. Emailed them again to confirm if it was fixed.
01/25/2018 – Received a generic email again from the customer care department asking for my account details and phone number to help me further.
09/21/2019 – As I never received an official response, my understanding is that this issue has been resolved. I’m writing this blog post for the general security awareness of my blog readers.